
Malcat tip: fast unpacking of RTF payloads
In this short tutorial, we will see how to extract binary payloads from RTF documents using Malcat. We will then proceed to emulate a shellcode for CVE-2017-11882 and extract the download link.
Read more →
Reversing a NSIS dropper using quick and dirty shellcode emulation
We will statically unpack and emulate a malicious NSIS installer running multiple shellcodes, up to the final Lokibot password stealer and its configuration.
Read more →
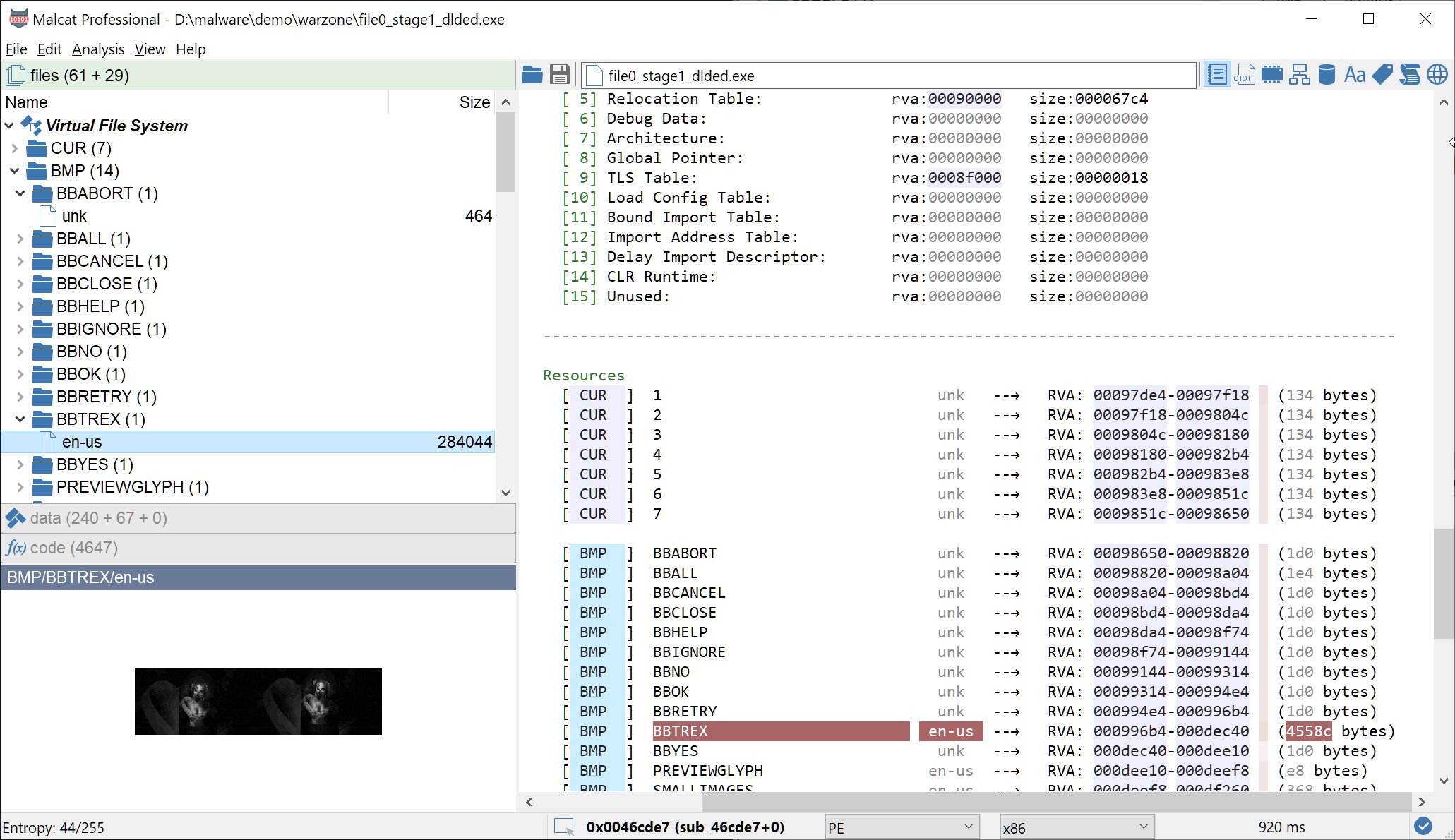
Exploit, steganography and Delphi: unpacking DBatLoader
We will unroll a maldoc spam exploiting CVE-2018-0798 leading to a multi-staged Delphi dropper abusing steganography and cloud services to conceal its payload
Read more →